Hunter DRP
Unified Digital Risk Protection & Identity Intelligence
Unmask external threats. Protect your brand. Neutralize identity risk across the Surface, Deep, and Dark Web.

How does Constella Hunter DRP (Digital Risk Protection) protect organizations?
Constella Hunter DRP provides comprehensive Digital Risk Protection by monitoring the surface, deep, and dark web for data leaks, brand impersonation, and exposed credentials. Unlike standard threat intelligence tools, Hunter DRP utilizes a Verified Identity Pedigree to link disparate data points, such as stolen session cookies and infostealer logs, back to specific corporate risks. This enables security teams to automate remediation for account takeover (ATO) and protect the organization’s digital footprint with 99% confidence.
Strategic Overview
The Intelligence Advantage
In a hyper-connected landscape, your organization’s risk isn't just on your servers, it’s being traded on criminal forums and Telegram channels. Hunter DRP acts as your external eyes and ears, providing 360-degree visibility into External Identity Risk. The platform is designed to handle the industrialized weaponization of identity data. We go beyond simple keyword alerts to deliver deep-context intelligence that allows SOC teams to move from "detection" to "attribution."
Real-Time Data Leak Detection
Instant alerts when credentials or sensitive documents appear on the dark web.
Infostealer Intelligence
Access to raw log files and stolen session cookies to prevent MFA bypass and session hijacking.
Brand Protection
Identify fraudulent domains, social media impersonations, and spoofed apps targeting your customers.
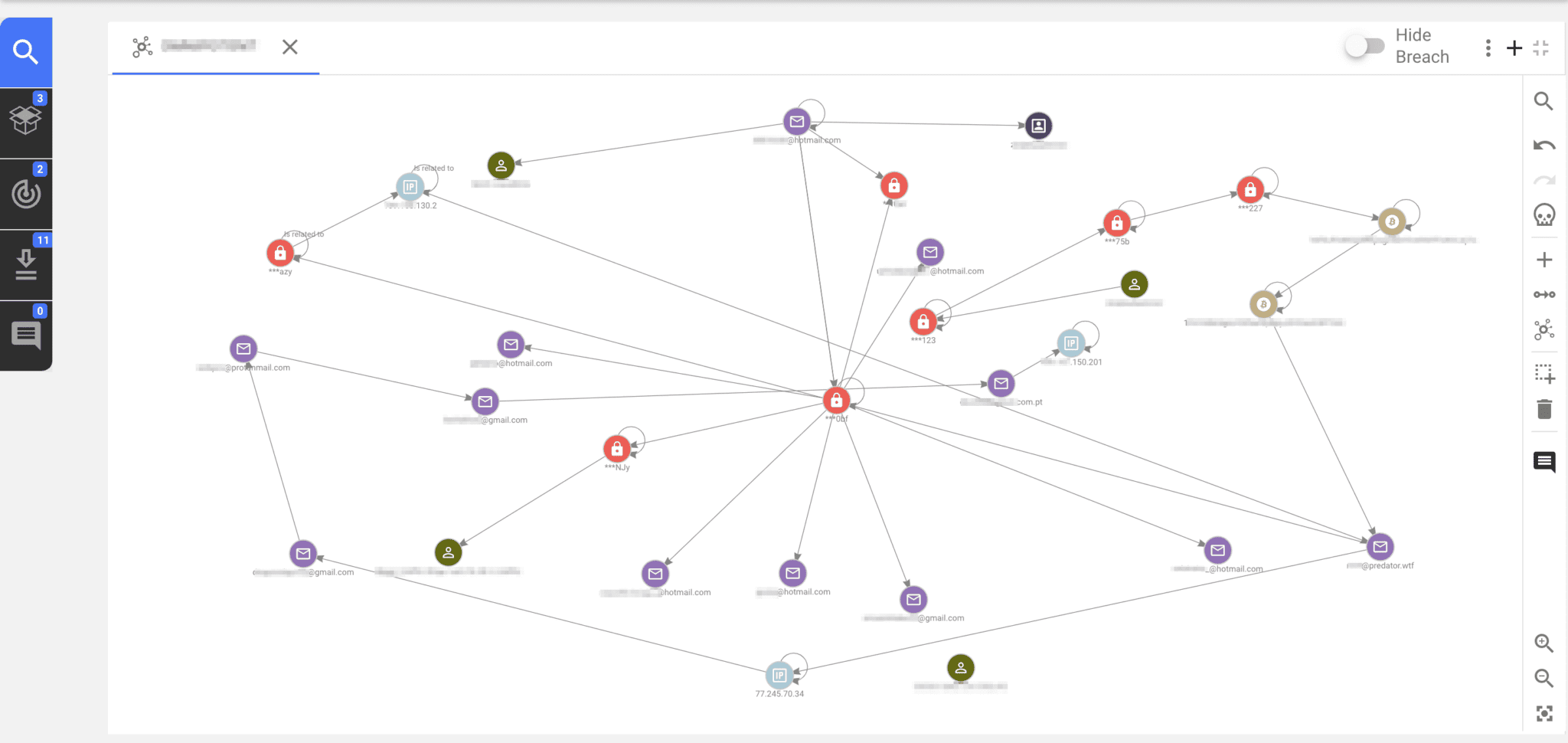
Identity Link Discovery
Use AI-powered tools to map connections between aliases, emails, and real-world threat actors.
Hunter DRP Product Alignment
Leveraging Constella’s enterprise-grade toolkit for total risk coverage.

Hunter Premium Platform
The central investigative command center for deep-dive forensics into breaches, pastes, and dark web content.

Hunter Copilot
An AI assistant that automates complex link discovery, reducing the time required to visualize threat actor networks by 75%.

Identity Fusion
The engine that verifies data pedigree, ensuring every alert is backed by authenticated identity attributes.

Maltego Transforms
Seamless integration for advanced link analysis and visualization of identity-to-threat relationships.
CASE STUDY
Rapid Ransomware Neutralization
The Challenge: A global manufacturing firm detected a series of unauthorized login attempts that bypassed their standard MFA protocols.
The Solution: The team utilized Hunter DRP’s Infostealer Search to identify 15 “hot” session cookies that had been harvested via RedLine malware and were being traded on a dark web marketplace.
The Result: By identifying the specific infected devices and invalidating the active sessions within 20 minutes, the firm thwarted a ransomware deployment that had already reached the internal reconnaissance phase.

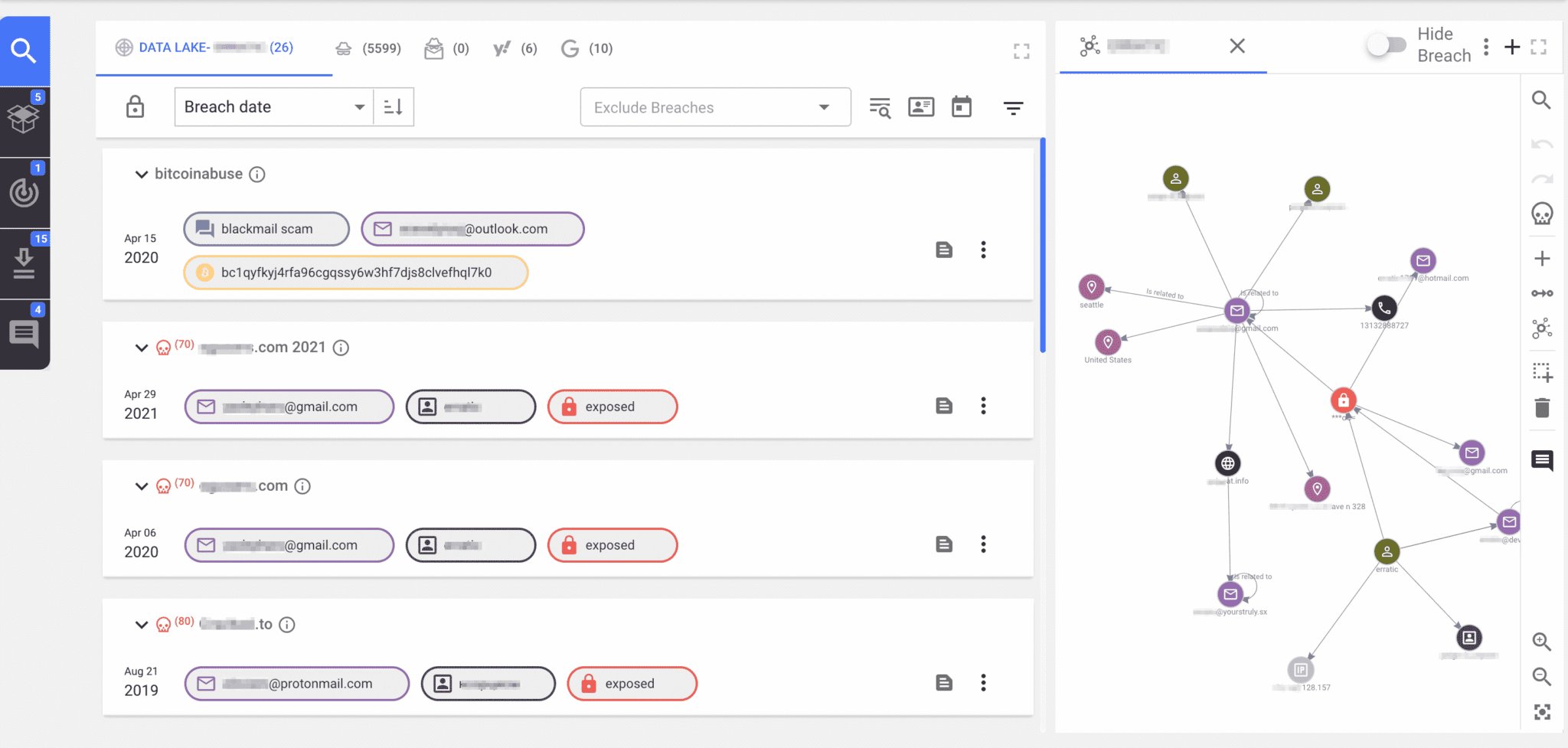
Visualizing the Risk
The Threat Map
A real-time visualization of your domain’s exposure across global criminal marketplaces.
The Identity Graph
A display showing how a single leaked employee password can be traced back to a specific malware infection and threat actor group.
One-Click Remediation
Integration with your SOAR or IAM tools to lock down exposed accounts the moment a leak is verified.
How It Works: The Identity Lifecycle
Constella follows a rigorous three-step framework to ensure organizational safety:
Collection
Aggregating billions of records from the Surface, Deep, and Dark Web.
Intelligence
Every record is deduplicated, timestamped, and verified through Identity Fusion.
Power
Verified alerts are pushed to your team for immediate remediation and attribution.