DEFEND YOUR DIGITAL PERIMETER
Identity Threat Intelligence Powered by Verified Breach Data
Constella boasts the world’s most curated Identity Risk Data, powering the next generation of risk models and investigative intelligence, including leading OSINT tools, enterprise risk protection, and high-velocity developer APIs.

What is Identity Risk Data?
Identity Risk Data is the collection of actionable intelligence derived from the surface, deep, and dark web that identifies compromised or vulnerable digital identities. Unlike static data, true Identity Risk Data includes a Verified Identity Pedigree, a combination of exfiltrated credentials, infostealer logs (such as stolen session cookies), and PII (Personally Identifiable Information) that has been cleaned and deduplicated.
This high-fidelity data allows security teams to move beyond simple breach alerts to proactively defend against account takeover (ATO), session hijacking, and ransomware by understanding the specific context and “freshness” of an exposure.

Why the World’s Top Brands Choose Constella
Our competitors, including most data brokers, sell unverified bulk dumps that create noise for your customers or SOC. Constella delivers Verified Pedigree.
1T+ Records Indexed
The world’s largest vetted identity database.
Source Transparency
We clean and verify every record to reduce false positives.
Real-Time Velocity
Fresh threat signals delivered via API.
The Dual-Platform Solution
IDENTITY DATA API
Data for Innovators
Seamless Integration. Massive Scale.
Power your customer-facing security or internal fraud detection engines with our high-speed API. Access the world’s largest library of compromised identity data through a single, secure endpoint.
- MDR/XDR – Power your detection stack with curated identity sets to catch “Pre-Ransomware” signals and session hijacking attempts that bypass traditional endpoints.
- Identity Theft Monitoring – Protect employees and customers with real-time dark web monitoring that flags stolen credentials the second they appear on criminal markets.
- OSINT – Accelerate investigations by linking anonymous digital fragments to verified personas, unmasking threat actors through high-fidelity data.
HUNTER+ (DRP)
Digital Risk Protection
Stop Identity-Based Attacks Before They Scale.
Hunter+ automates the detection of compromised credentials, brand impersonations, and executive risks. Protect your VIPs and your workforce with a platform designed for the modern SOC.
- Executive Protection – Secure leadership by monitoring personal digital footprints. Identify PII leaks and infostealer infections on private accounts.
- Brand Integrity – Defend your reputation with automated takedowns of phishing sites and rogue profiles. Unmask the threat actors behind impersonation.
- Ransomware Prevention – Neutralize the primary entry point: stolen credentials and hijacked cookies. Identify “Pre-Ransomware” signals in infostealer logs.
Built for Your Industry’s Toughest Challenges.
Financial Services
Protect accounts and satisfy strict regulatory compliance (GDPR/SOC2).
Public Sector
Advanced OSINT and investigative tools for law enforcement and government.
Retail / E-Commerce
Defend against credential stuffing and loyalty program fraud.


FEATURED RESOURCE
2026 Identity Breach Report: 107 Billion Records Exposed
Download our latest research to see how infostealers and AI are revolutionizing the cybercriminal underworld.
Insights from the Front Lines of Identity Risk
Stay ahead of emerging threats with proprietary research and actionable analysis from the Constella Intelligence Team.
Frequently Asked Questions
Identity risk intelligence is the practice of continuously monitoring, analyzing, and acting on data about compromised or exposed digital identities across the surface, deep, and dark web. Unlike basic breach monitoring, which alerts you after the fact, identity risk intelligence provides the context, freshness, and provenance of each exposure — enabling security teams to prioritize and respond before an attacker can exploit stolen credentials, session cookies, or PII.
Standard dark web monitoring tools scan known forums and marketplaces for keyword mentions of your domain or email addresses. Constella goes further by ingesting, cleaning, and verifying breach data at scale — 54.6 billion curated records across 125+ countries and 50+ languages. Where other tools surface alerts, Constella delivers verified identity context: what was exposed, when, from which source, and how likely it is to be weaponized. That difference determines whether your team chases noise or acts on signal.
An infostealer is a category of malware designed to silently harvest credentials, session cookies, autofill data, and browser history from an infected device. Unlike traditional breaches that expose stored passwords, infostealers capture live session tokens — allowing attackers to bypass multi-factor authentication entirely. Constella processed 51.7 million infostealer packages in 2025, a 72% year-over-year increase. Organizations that do not monitor for infostealer-sourced exposure are effectively blind to one of the fastest-growing attack vectors targeting enterprise identity.
Constella serves two distinct buyer needs. The Build path (Identity Data API) is for product owners, MDR/XDR platforms, fraud teams, and developers who need to embed high-fidelity identity risk data directly into their own products or detection engines. The Investigate path (Hunter+ DRP platform) is for security teams, CISOs, and OSINT analysts who need a ready-to-use platform for threat investigation, executive protection, brand monitoring, and digital risk protection. Both paths draw from the same verified data foundation.
Every record in Constella’s database is processed through a multi-stage verification pipeline that cleans, deduplicates, and enriches raw breach data with source provenance. This means Constella can tell you not just that a credential was exposed, but where it came from, how recently, and how many times it has been recycled across subsequent breach compilations. This verified pedigree is what separates actionable intelligence from raw data volume.
Constella’s identity risk intelligence is deployed across financial services, telecommunications, retail and e-commerce, public sector, law enforcement, and managed security service providers (MSSPs). Any organization that manages digital identities at scale — or that needs to attribute threat actors and investigate identity-based attacks — is a fit for one or both of Constella’s product paths.
Account takeover is a form of identity fraud in which an attacker uses stolen credentials or session tokens to gain unauthorized access to a user’s account — bypassing passwords and MFA. Constella detects ATO risk by monitoring for newly exposed credentials and active infostealer logs tied to your domain, alerting security teams the moment an employee or customer identity appears in criminal markets. This pre-exploitation signal window is where ATO is stopped.
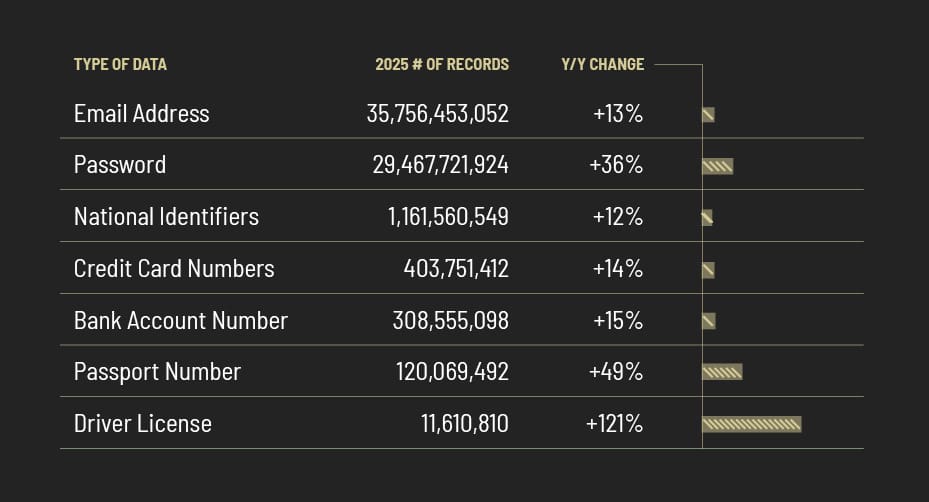
Our platform is powered by the verified classification of billions of breached records—spanning credentials, financial data, government identifiers, and sensitive personal information worldwide.
Ready to Mitigate Identity Risk?
Join the organizations that rely on Constella to turn raw data into decisive action.