Stop chasing data. Hunter moves security and investigation teams beyond alerts and raw breach records: delivering clarity, attribution, and foresight from fragmented digital identity signals.

INTO DECISIVE INTELLIGENCE
Stop chasing data. Hunter moves security and investigation teams beyond alerts and raw breach records: delivering clarity, attribution, and foresight from fragmented digital identity signals.

IDENTITY IS THE NEW ATTACK SURFACE
More than 50% of ransomware attacks originate from infostealer infections — not exploits. Hunter centers your security posture around identity exposure: surfacing how credentials, behavior, and access intersect before attackers can act on what they know.
State-sponsored groups and criminal actors around the globe are actively harvesting credentials targeting energy grids, financial systems, insurance carriers, and government infrastructure. Hunter reveals risk where attacks really begin.
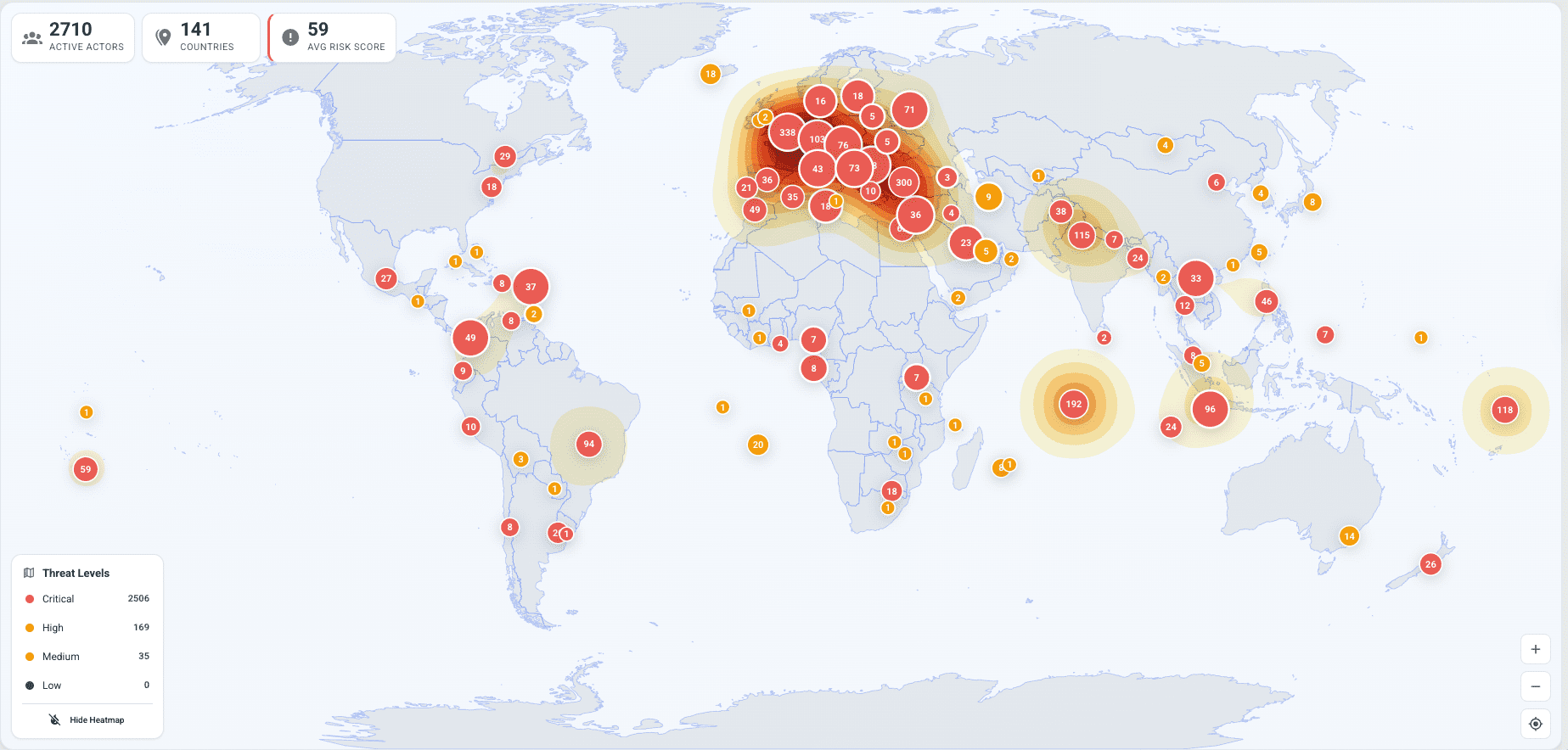
Most tools show you victims. Hunter identifies the threat actors hiding inside that victim data — flagged by visits to criminal forums, dark web markets, and malicious infrastructure. Classified into Critical, High, and Medium tiers with full forum identity mapping. See the actor, not just the artifact.
REAL-TIME · 60-DAY FRESHNESS
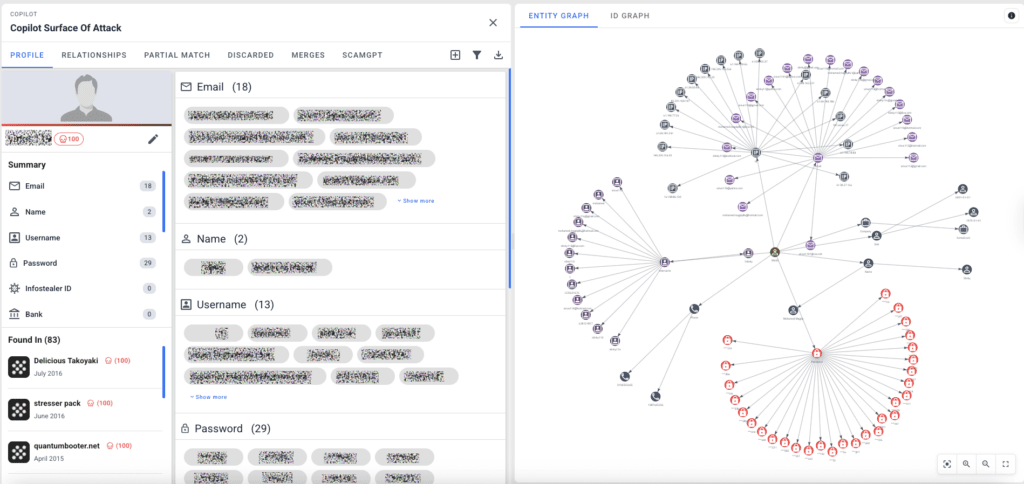
Paste any starting point — a LinkedIn URL, email, username, or phone number. Copilot runs automated identity fusion across Hunter’s full dataset: credentials, cookies, browser history, platform aliases, and behavioral signals. Investigations that take analysts 30–120 minutes complete in seconds.
INVESTIGATE IN SECONDS, NOT HOURS
Raw logs are noise. Hunter’s insight layer classifies cookies by active vs. expired status, detects corporate credential reuse, surfaces search intent from browser history, and maps infection metadata into investigation-ready intelligence. Eliminates manual correlation and analyst guesswork.
FROM RAW DATA TO REAL INTELLIGENCE
Search any domain or IP across fresh infostealer packages to detect whether it was accessed by a compromised device. Know before a threat actor buys the credential to your energy system, financial portal, or government network. Hunter detects infostealer-driven attacks before ransomware hits.
SEE THE ATTACK BEFORE IT HAPPENS
Browser history and search data inside infostealer packages reveal what a threat actor was planning — travel research, affiliate reconnaissance, target selection. Hunter doesn’t just tell you who they are. It tells you what they’re preparing. Know the actor’s intent, not just their identity.
KNOW WHO THEY ARE — AND WHAT THEY’RE PLANNING
NORTH AFRICA · CRITICAL ACTOR · BLURRED PII
A Critical-rated threat actor operating out of Rabat, Morocco was identified through Hunter’s Adversary View — active on Nulled, cracked.io, BlackHatWorld, and HackForums, targeting financial institutions with harvested credentials. Hunter’s Copilot ran a full automated investigation from a single starting point.
Investigations that take law enforcement analysts 30 minutes to two hours — and competing platforms at $500K+/year even longer — Hunter completed in seconds. Accelerating attribution by unifying identity signals into clear, defensible intelligence.

 PII blurred in compliance with privacy protocols. Actual platform shows full identity data.
PII blurred in compliance with privacy protocols. Actual platform shows full identity data.
Unmask threat actors in seconds.
Accelerates attribution by unifying identity signals into clear, defensible intelligence. Used by agencies across Germany, Denmark, Switzerland, Spain, France, Italy, Portugal, and Europol.
Detect infostealer-driven attacks before ransomware hits.
Hunter reveals identity-driven risk earlier — so CISOs and threat intelligence teams at energy, finance, insurance, and healthcare organizations can act before exposure becomes impact.
Follow the money through digital identity, not spreadsheets.
Hunter connects digital identities across accounts, devices, forums, and wallets — helping fraud and AML teams uncover hidden relationships and reconstruct full financial crime footprints, faster.
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
REQUEST A DEMO
In 30 minutes, our team will show you exactly how Hunter converts exposed identity data into decisive intelligence — using live data relevant to your sector, not slides. Walk through the Adversary Map, watch Copilot build a full identity graph in real time, and see why teams across law enforcement, enterprise security, and financial crime choose Hunter.
For additional information about how Hunter is being used in real investigations, we invite you to read the Krebs on Security blogs.