
The Hidden Identity Risk in Your Third-Party Ecosystem
Your Security Program Is Only as Strong as the Identities Connected to It Organizations have invested heavily in securing their internal environments. They deploy identity

Your Security Program Is Only as Strong as the Identities Connected to It Organizations have invested heavily in securing their internal environments. They deploy identity

The shift to stolen sessions no one is talking about enough For years, cybersecurity conversations around identity risk have focused on one thing: Passwords. Weak

Account takeover is no longer a perimeter problem Account takeover (ATO) has become one of the most persistent and costly forms of fraud. And yet,

Intelligence without action doesn’t reduce risk Over the past few years, organizations have made significant investments in data and intelligence: Threat intelligence feeds Monitoring tools

Recap of the live panel hosted by Constella and WMC Global on April 30, 2026 ▶ Watch the full recording If you’ve gotten a text

Introduction: Two terms, one growing confusion In cybersecurity conversations today, two terms are showing up more frequently: Threat Intelligence Identity Risk Intelligence At a glance,
Mobile fraud losses are projected to decline in 2026. That headline is technically accurate and deeply misleading. The fraud is not going away. It is
Here Is What That Looks Like From an Investigator’s Perspective. The DPRK remote IT worker scheme is not a cybersecurity problem. It is an identity

The problem with how we monitor identity risk today For years, dark web monitoring has been positioned as the frontline defense against compromised credentials and
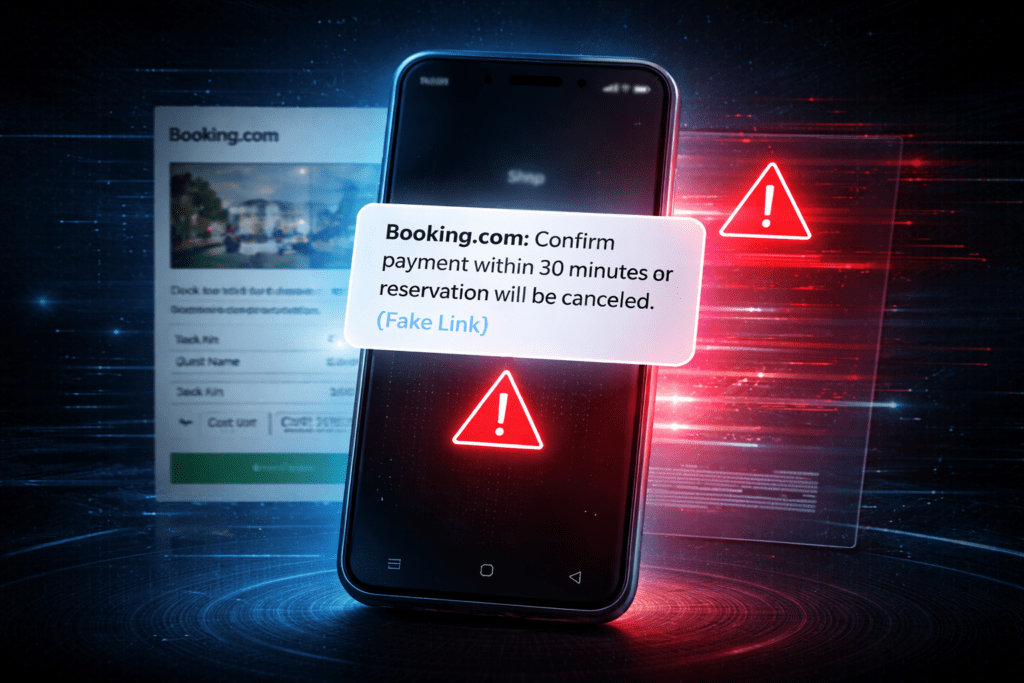
Booking.com’s breach exposed names, phone numbers, and booking details now being used in targeted WhatsApp phishing. Constella explains how the PII-to-smishing pipeline works and what to do about it.

A new category is emerging in cybersecurity For years, organizations have relied on monitoring tools to detect compromised credentials and exposed data. But as identity

Google’s Device Bound Session Credentials are a meaningful step forward against infostealer malware. They also have significant limits that security teams need to understand before