
Smishing at Scale: What Our Expert Panel Revealed About the Mobile Phishing Supply Chain
Recap of the live panel hosted by Constella and WMC Global on April 30, 2026 ▶ Watch the full recording If you’ve gotten a text

Recap of the live panel hosted by Constella and WMC Global on April 30, 2026 ▶ Watch the full recording If you’ve gotten a text
Mobile fraud losses are projected to decline in 2026. That headline is technically accurate and deeply misleading. The fraud is not going away. It is
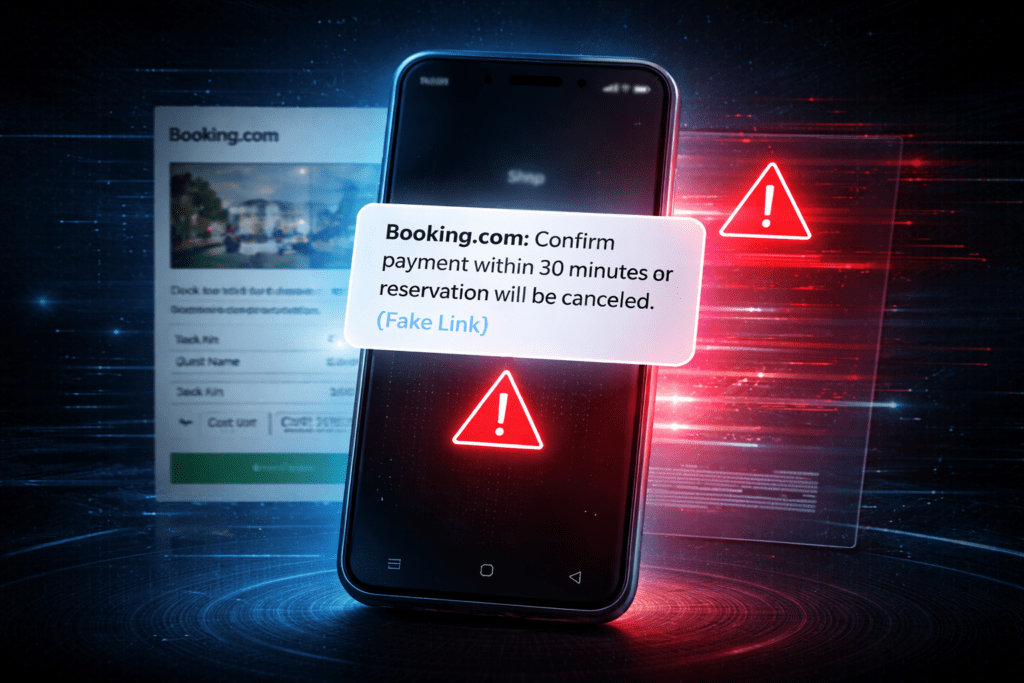
Booking.com’s breach exposed names, phone numbers, and booking details now being used in targeted WhatsApp phishing. Constella explains how the PII-to-smishing pipeline works and what to do about it.

Google’s Device Bound Session Credentials are a meaningful step forward against infostealer malware. They also have significant limits that security teams need to understand before
78% of recently breached organizations had corporate credentials sitting in infostealer logs before the breach was ever detected. The 48-hour window is not a countdown

Iranian state-linked hackers published emails stolen from FBI Director Kash Patel’s personal account. The lesson for every security leader: no title protects you from an

Exposure monitoring has become a core function for security and risk teams but many programs still struggle to deliver clear, actionable outcomes. Alerts pile up,

Compromised credentials are the primary entry point for ransomware, account takeover, and business email compromise. Monitoring for exposed credentials continuously and acting on detections before
Dark web monitoring is the continuous process of scanning hidden adversary channels for stolen credentials, exposed employee data, and organizational intelligence that threat actors collect

A compromised credential is the starting point for most enterprise breaches. Detecting it early, before an attacker purchases and uses it, is the difference between

Credential monitoring detects when employee or organizational credentials are exposed in the adversary ecosystem, enabling security teams to respond before those credentials are used to
2026 is going to be a strange year in cybersecurity. Not only will it be more of the same, but bigger and louder. It stands