Growing Cyber Threats Focus on Ransomware, Infostealers, and Defacements
This blog continues our geopolitical series, highlighting the growing cyber threats during the ongoing Israel-Palestine tensions. Recent months have seen a significant increase in cyberattacks targeting Israeli institutions, with a particular focus on ransomware, infostealers, and defacements. This blog delves into the most recent incidents, primarily orchestrated by the Handala group.
Escalation of Tensions in Israel
As mentioned in our previous blog, the escalating tensions between Israel and Palestine are mirrored in cyberspace by increased activity from the Handala Hack Group. Active since 2011, this pro-Palestinian hacker collective has intensified its cyber offensives against Israeli targets, employing defacements and ransomware attacks to disrupt operations and steal sensitive information. These attacks not only aim to cause financial and operational damage but also to broadcast their political message and gain support against Israel.
Recent Ransomware Attacks by Handala
Handala has potentially conducted numerous ransomware attacks, targeting the technology, education, and healthcare sectors. Here are some of the most recent incidents:
- On May 27, 2024, Zionist Information Technology was potentially attacked.
- The affected entities include Cello (formerly Cellopark), MER Group, ForSight Robotics, Magnet Accelerator, Citizen Café Tel Aviv, Toks, Barak Finance, EasyUP, Sirius Electronics, Israel Archaeological Services, and Shai Nursing Company.
- This attack compromised multiple sectors, including technology, healthcare, and academic services, highlighting significant breaches in Israeli cybersecurity.
- Ramat Gan Academic College faced a possible attack on May 25, 2024, affecting its educational infrastructure and data.
- Harmony Pharm, the largest pharmacy in Tel Aviv, was attacked on May 22, 2024, disrupting the pharmaceutical supply chain.
- Amigour Company, a major housing and community development company, was hacked on May 16, 2024. The attack led to 522 GB of data being dumped and wiped.
- High Group, a key settlement development source, was attacked on May 2, 2024, resulting in 84 GB of data being dumped.
Defacement Attacks: Exposing the Faces of Cyber Warfare
A defacement attack involves altering the visual appearance of a website, often to display a political or social message. Handala Group and other hacktivist groups have been actively engaging in defacement attacks to criticize and expose Israeli entities publicly.
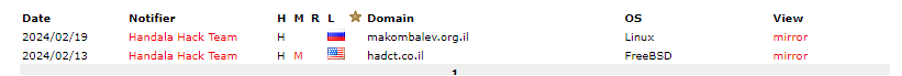
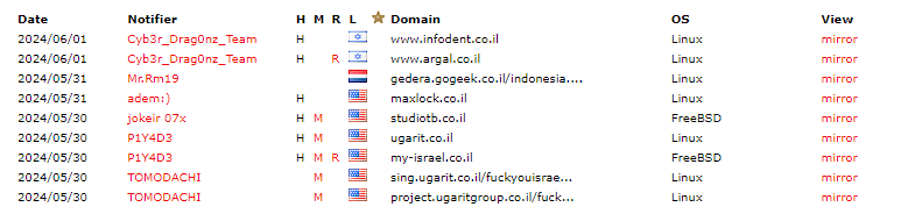
Here are some notable recent defacements:
- Handala Group: Two defacements recorded on makombelev.org.il and hadct.co.il
- Cyb3r_Drag0nz_Team: Defaced www.infodent.co.il and www.argal.co.il
- Mr.Rm19: Targeted gedera.gogeek.co.il
- adem:): Defaced maxlock.co.il
- jokeir 07x: Targeted tudiotb.co.il and ugarit.co.il
- P1Y4D3: Defaced multiple pages under ugaritgroup.co.il
- TOMODACHI: Defaced call.ugarit.co.il and mishkan-store.co.il
- ./r0cky_n00bz: Targeted horoot.co.il
- Cyber Ghost: Defaced hadpeami.co.il, korki-net.co.il, and shoo-fee.org.il
- DragonForceMalaysia: Defaced bridgesalon.co.il
- Hacktivist Indonesia: Targeted isr.org.il
- JH-TEAM H: Multiple defacements including www.nsc.org.il and maccabi.co.il
- the key40: Targeted maccabi.co.il
- systemadminbd: Defaced www.ite-cat.co.il
Infostealer Infections: A Growing Concern
The data previously exposed in ransomware attacks could lead to further infections by infostealers. Infostealers are malware designed to gather sensitive information from infected systems, such as login credentials and personal data.
- Smart College
- 99 Digital
- Ramat Gan Academic College
- Barak Finance
These infections could be the root cause of some of the previous ransomware attacks or, even worse, could be used to enhance the damage of the existing ones.
Conclusions and Recommendations
The recent surge in cyber attacks amid the Israel-Palestine conflict underscores the evolving nature of digital warfare. Ransomware, infostealers, and defacements are being utilized to disrupt, expose, and damage critical sectors in Israel. Understanding these threats is crucial for mitigating the impact of these malicious activities.
Recommendations:
- Be Careful with Emails: Avoid clicking links or downloading attachments from unknown or unsolicited emails. Phishing is a common method hackers use to access personal information.
- Use Two-Factor Authentication (2FA): Enable 2FA on all accounts to add an extra layer of security.
- Regularly Update Systems: Keep all software and systems up to date with the latest security patches to prevent exploitation of known vulnerabilities.
By adopting these practices, individuals can significantly reduce their risk of falling victim to cyberattacks and ensure a robust defense against the ever-evolving threat landscape.
