The Spbglobal and Gocco Ransomware Incident and its Broader Implications
In a digital era where data breaches have become almost a daily occurrence, the recent ransomware incident on spbglobal.com and gocco.com by the notorious “Cactus” group has raised alarms across the cybersecurity landscape. This ransomware incident, disclosed through a post on their dark web site, not only highlights the persistent threat of ransomware but also underscores the dangers of personal information exposure, especially when high-quality national IDs and sensitive personal data are involved.
The Risks of Exposed Personal Information
The exposure of personal information, such as high-quality images of national IDs, presents a goldmine for cybercriminals. Such data can be exploited in a myriad of malicious ways. Impersonation becomes trivial; a threat actor can easily assume the identity of a victim to commit fraud, apply for credit, or even create online services and accounts in the victim’s name. The ramifications of this can be devastating, affecting victims’ financial health, reputation, and privacy.

Enriched Data: A Double-Edged Sword
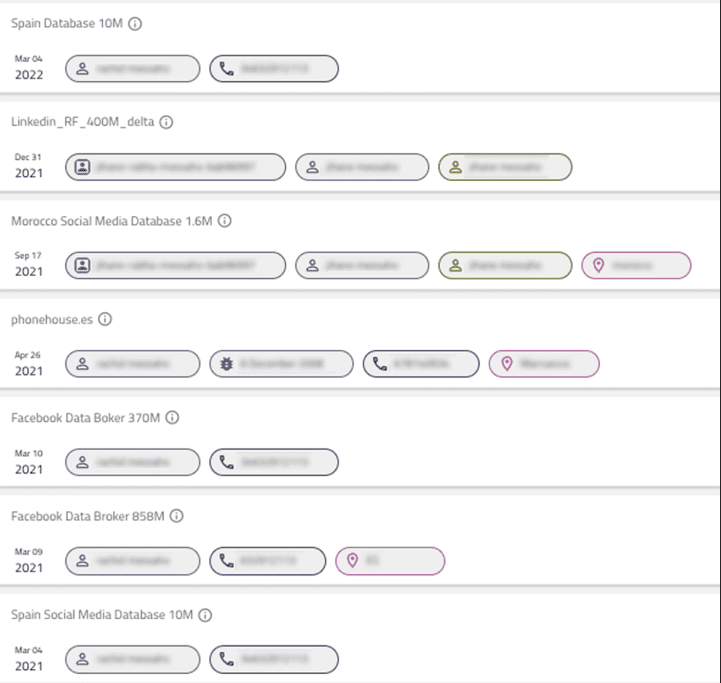
Our preliminary investigation into the exposed identities has revealed a concerning trend: many of the victims’ data were also compromised in previous, well-known data breaches i.e phonehouse.es, scrapped data from LinkedIn, Data broker sites, etc. (Some screenshots from our Hunter tool)
This enriched data set amplifies the risks significantly. Cybercriminals can leverage the combination of fresh ransomware-exposed data and previously breached information to conduct more sophisticated attacks. For instance, using exposed phone numbers, they can launch targeted SMS phishing (smishing) or voice phishing (vishing) campaigns, tricking victims into revealing additional sensitive information or installing malware on their devices.
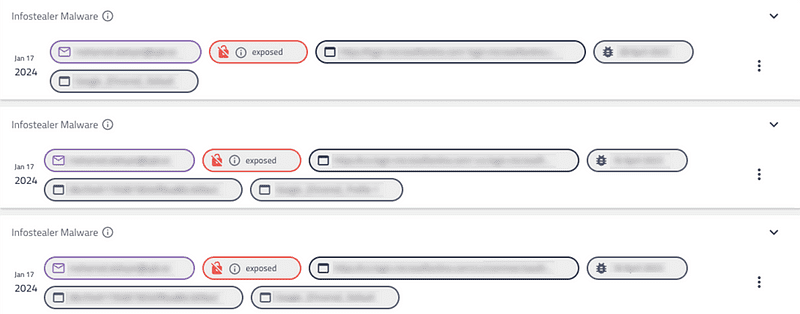
Our investigation further revealed that both domains were compromised in previous breaches, making it alarmingly straightforward to access numerous plaintext passwords of potential employees. Even more concerning, both were also exposed in infostealer infections, once again linked to potential employees. This significant security oversight may very well be the root cause of the recent attack.
The AI Factor: Amplifying the Ransomware Incident Threat
The advent of AI adds another layer of complexity to the situation. With access to high-quality images and personal details, threat actors can use AI to generate fake, yet highly realistic, documents or identities. This not only expands the surface of attack but also makes it increasingly difficult to distinguish between legitimate and fraudulent identities. The potential for misuse in these ransomware incident scenarios such as deepfake creation, synthetic identity fraud, and more is immense, making it a pressing concern for individuals and organizations alike.
Protecting Identities in the Digital Age
In response to these escalating ransomware incidents, Constella Intelligence has positioned itself as a bulwark against identity theft and cyber fraud. By identifying, curating, and analyzing exposed information across the internet, Constella provides a comprehensive defense mechanism. Their proactive approach to monitoring the dark web, forums, and other digital avenues for leaked or stolen data helps mitigate risks before they can be exploited by cybercriminals.
Our efforts, as a company, are crucial in the current cybersecurity landscape, where the sophistication and frequency of attacks continue to grow. Our work not only aids in immediate threat neutralization but also in building long-term resilience against identity theft and fraud.
Conclusion
The ransomware incident on spbglobal.com and gocco.com by the “Cactus” group is a stark reminder of the vulnerabilities inherent in our digital world. As individuals and organizations navigate these treacherous waters, it’s imperative to remain vigilant and proactive in protecting personal information.


